Human Practices Gold
In this section, we explore how we integrated the results of Human Practices into CryptoGErM.
We got in contact with experts from National Institutions, we performed a global survey and we consulted the requirements of a potential user.
We conducted a research of the national and international legislations for the shipping of GMOs.
Finally, we dedicated our Educational activities to receive students in our laboratory to do experiments and funny activities
You can find more details of this Integrated Human Practices Projects below by clicking on the tiles!

Social
“Human Practices is the study of how your work affects the world, and how the world affects your work.” - Peter Carr
In this part of Human Practices of CryptoGErM, we decided to get in contact with the main audiences that we consider important for the realization and execution of our project:
- National Institutions: What are the current challenges that the experts in the field have to overcome in the area of encryption and cybersecurity?
- Potential Users: What are the current requirements that a potential user of CryptoGErM needs?
- Society: What is the current perception about cybersecurity among society in general and how can we get them closer to our project and synthetic biology?
National institutions
National Cyber Security Center from the Ministry of Security and Justice of the Netherlands
We got in contact with the National Cyber Security Centre (Nationaal Cyber Security Centrum, NSCS) from the Ministry of Security and Justice of the Netherlands, in order to understand what the current challenges and requirements in the development of a system for the storing and sending of sensitive information are. Such requirements are important for our project since we are able to have a clear idea of the actual and real application of CryptoGErM.
The feedback received from the NCSC relies in trying to solve two problems that are present each time that the storing and sending of sensitive information is intended. The difficulty, according with the comments from the National Cyber Security Center, in securing stored information generally does not lie with the encryption methods, but rather with two other problems:

How we propose to approach these problems:
To make it especially hard for unauthorized parties to access our key, the key-spores will be sent in a mixture of decoy spores. The decoy is present in a much higher ratio than the key-spores. The key-spores have to be recovered using a specific selection mechanism. We have developed a ciprofloxacin resistance cassette that can be integrated into the B. subtilis genome. Only the knowledge of this specific selection antibiotic will allow the recovery. To access the key not only general knowledge about molecular biology is required. The recipient has to know specific information about the exact biological procedure that has to be applied in order to access the key.
We believe that getting in contact with the National Institutions in charge of the protection of digital information, gave us a better understanding of what professionals and experts might expect from our project.
Potential users
Groningen Archives
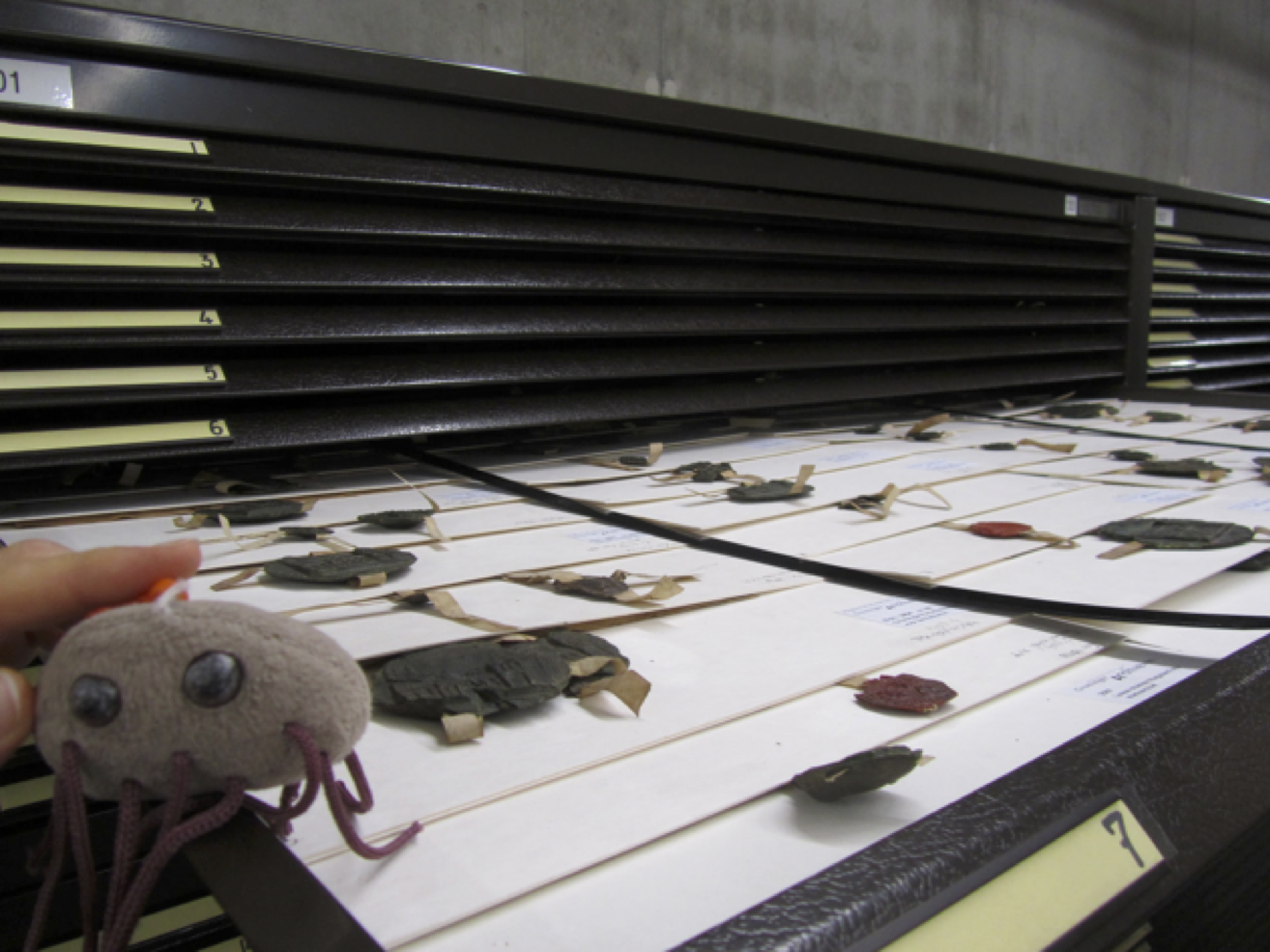
CryptoGErM is a project focused on the storing of potentially large encrypted data to ensure its protection and durability, and subsequent shipping by conventional means... In order to understand what the currents systems for the storing of data are and how CryptoGErM could be used by Private and Public Institutions for the storing and preserving of their information, we got in contact with the Groningen Archives!


The Regionaal Historisch Centrum Groningen Archieven is the information centre for the History of the city and the province of Groningen. Files, books, newspapers, maps, photos, films, videos, and voice recordings are stored and tell the story from the province of Groningen from the Middle Ages until now.
We learned that the Groninger Archives store the old administrations of the State Institutions of the province of Groningen, besides that, they also manage the archives of families, churches, societies and private companies.
Currently in the Groningen Archives, most of the information is stored on special, high quality paper, although other storing means are used such as tapes, CD’s, DVD’s for multimedia (films and audio recordings). However, for that type of storing, specific conditions are required to ensure the correct and long preservation of the paper, i.e. a specific temperature (18°C) in dry air carton boxes. Within the Groningen Archives the air composition and quality paper is controlled by a system in the building because the presence of acid in paper, that can come either from air or plastic, is the most common reason of disruption of the stored paper. We found out that if it is true that on the one hand, even with the right conditions the low quality paper (for example from newspapers) cannot be stored for a long time (a few decades), it is also true that by taking right and strict controlled conditions some high quality papers can be stored for even hundred of years.
This is why, for 20 years the Groningen Archives has been preparing for the change from analogous data storage to digital data storage.
“Two things are important: the storability and the accessibility” - Jan Jaap Hoogstins
“DNA in spores is a considerable option (for the storing of information) if the information does not change through mutations” - Jan Jaap Hoogstins
According to Jan Jaap Hoogstins, collection manager from the Groninger Archieven, the nature of the medium used for the storing does not matter as long as it is insured that the stored information is completely preserved. For him, “DNA in spores is a considerable option if the information does not change through mutations”
As result of this interview we found out that our system can be used for such Institutions for the long-term storing of information, according to Jan Jaap Hoogstins, “there is no system yet that stores information forever in an entirely preserved manner”
However, Jan Jaap Hoogstins insisted that the bacteria must not present mutations…
In order to consider this problem CryptoGErM has done some research and modelling about it!
We found out that it is unlikely that there are mutations in the message stored in our system. For more details and full description please go here.

Society
Survey
We performed a survey to understand what the current perception about digital and physical storing of information is among different sectors of society.
The survey was designed together with one specialist, in order to adapt it with the requirements and professionalism that the conduction of a survey requires.
Our survey studies the following points:
- The current perception about the storing of sensitive information
- What is the impression of sending information through conventional means
- How the nationality influences the perception of digital and physical storing of information
To achieve the aims of the survey mentioned above, we planned to reach as many people as possible from different countries and different ages. By looking to previous surveys conducted for former iGEM Teams, we have found out that most of the surveys carried on were mostly in English, thus their results would be limited exclusively to English-speakers. However, how about the people that use social media but do not speak English?
CryptoGErM is also interested in their opinion! They are important to us!
We invited iGEM Teams to share the survey on their social media in order to achieve as many people as possible. In addition to that, we collaborated with iGEM Teams around the world that translated the original survey to their native languages. We have versions in English , Chinese and Spanish.
The following map shows the nationalities of the participants involved in the present survey:

Firstly, we asked our survey respondents which is the most frequent method that they use to send sensitive information. As depicted in Graph 1, 89% of the people send information through digital means (Email, social media and instant messaging apps) Likely because of the speed and accessibility that these communication means provide to the user when compared towards physical sending (Regular Post).
In addition to that, 50% of the people who answered our survey trust sending their information through regular post and email, while 33% trust only one between the two mentioned methods. 17% of the population does not trust sending information by any of the methods mentioned above. This is summarized in Graph 2


From the two questions above, we formulated an initial conclusion: Survey respondents use and trust digital and physical means for sending of information.
However, what would happen if they might need to send highly secure information. Would they trust current and conventional methods such as a letter in regular post or an email? How would their initial conclusion change when the information that has to be sent would change from hardly secret to highly secret?
The answers to these questions are the first point of interest of the study: What is the current perception in the sending of sensitive information?
We found out, by asking to our survey respondents if they would send highly-secret information by regular mail or email (Graph 3), that 46% of the population would not trust sending such information through those conventional means (either by post or email) 39% commented that it would depend on the destination of the information. Survey respondents commented that the locations where the post service is efficient and reliable, could be considered as an option: however, in places where such systems are not completely efficient, they would not consider it as an option.
By analyzing deeply each individual responses we found out that 84% of the survey respondents that would not trust to send sensitive information through conventional means belong mostly to Latin American countries (taking only into account the nationality of the survey respondents: Mexico, Brazil, Guatemala and Costa Rica) In contrast, most of the percentage of the people who trust sending such information by both post and email correspond to European Countries. It might be that in Latin American countries the efficiency of the post is low compared with the European service. We truly believe that the improvement of the current post services in Latin American countries will lead to an enhancement of the current postal services, and also will open the market to our system in a near future.
“89% of the survey respondents send information through digital means, but 46% would not do it if it is highly-secure information”
But such a low trust is not limited only by the physical means of sending. Actually it is more pronounced when it comes to the digital storing and sending of information. From the total of our survey respondents, 76% does not feel that the information on the internet is safe from digital espionage. (Graph 4)


“What is contrasting is that 89% of the survey respondents use digital means to send information, but 76% consider that such information is not safe from digital espionage”
Actually, according to our surveys respondents, private companies are the principal target from digital espionage (the aim of the digital espionage is to obtain information) and consequently of the theft of information (theft of information “occurs when attackers steal data with the aim of selling these data for commercial gain, to publish them or to abuse them for activist purposes”) As depicted in Graph 5, for our survey respondents, governments are the next most popular target of digital espionage, and citizens are the less popular sector affected for digital espionage and theft of information.

However, the reality is a little bit different when we compare these results with the data published by the Cyber Security Assessment Netherlands CSAN 2015 from the National Cyber Security Centre from the Ministry of Security and Justice from the Netherlands. For professional criminals, as the source of the threat, “there are clear developments which make the threat expedient” against private organisations and citizens, making these two sectors the principal targets of digital espionage and theft of information, In the case of Governments, either phenomena of threats have been observed or there are sufficient measures to remove the threat.
Since the aim of the digital espionage is to obtain and steal information from digital sources, we asked our survey respondents how they store their information. Surprisingly we found out that 57% of them store sensitive information either physically or digitally while the remaining 43% do not store it. Survey respondents commented that they do not store them because they are afraid of being hacked. On the other side, the physical storing is not used because of the possibility to be stolen. (Graph 6)


Now that we know that almost half percent of our survey respondents do not store information because they are afraid of being hacked, we asked them if they would trust storing their sensitive information in bacteria.
As depicted in Graph 7, 43% of the survey respondents would trust to store information within bacteria, which shows that CryptoGErM could be used by citizens as a storing method.
However, an outstanding amount of 26% of the survey respondents answered that they did not know what bacteria were. This result motivated us to reach as much people as possible by focusing our Human Practices on the promotion of synthetic biology besides our project itself.
As a consequence the actions of the educational and outreach sections of CryptoGErM were focused to reduce the amount of people that do not what bacteria are, by promoting the knowledge of synthetic biology, the iGEM competition and of course our project. This has been done through media, conferences, invitation of students to join our lab work and by receiving students from High Schools for a lecture of Bio-ART: Painting with Bacteria!
Please consult our Educational and Outreach Section to discover our activities!
Legal
”You can’t build a society without law” - Naftali Bennett
Our project is oriented to the safe sending of encrypted information through conventional means (such as regular post) rather than only on the pure storage in bacteria. For that we are providing the Bacillus subtilis spores with several biologic layers.
In this part of Human Practices, we explore the current national and international legislations that the CryptoGErM system must obey in order to ensure its safe and unrestricted shipping.
National Legislations
With the advising of the National Institute for Public Health and the Environment (Rijksinstituut voor Volksgezondheid en Milieu; RIVM) from the Ministry of Health, Welfare and Sport from the Netherlands we consulted the current national law requirements and international legislations that regulate the sending of Genetically Modified Organisms (GMOs).
Currently, the shipping of GMOs is strictly regulated in The Netherlands.
Such regulations are stated in the articles 3rd and 4th from the Environmental Regulation of Genetically Modified Organisms (Regeling genetisch gemodificeerde organismen milieubeheer 2013) [1]. These articles state the norms for the deliberate shiping of GMOs within the Netherlands; if the shiping of the Bacillus subtilis spores from the CryptoGErM system is intended within the Netherlands, it must obey this legislation.

According to these articles, “the shipping of Genetically Modified Organism within an Institute, or aboard a ship, must occur in accordance with the following guidelines”
- GMOs must be transferred in a closed, unbreakable, non leaking containers
- Containers of GMOs must be disinfected before shipping
- The dispersion of GMOs to the environment must be avoided by applying the relevant safety measures.
We applied these regulations for the design of the shipping container used for the sending of CryptoGErM spores.
International Legislations
The next step was looking for international laws that regulate the shipping of GMOs around the world, since one of the applications of CryptoGErM is the shipping of Bacillus subtilis spores containing sensitive information across borders.
European legislations
Firstly, we were interested in the European legislations regarding the shipping of GMOs; it was found out that several European Countries, including the Netherlands, follow the regulations and guidelines suggested by the Cartagena Protocol for the transboundary shipment of Genetically Modified Organisms.
But what is it the Cartagena Protocol?
The Cartagena Protocol on Biosafety to the Convention on Biological Diversity is an international agreement on biosafety as a supplement to the Convention on Biological Diversity, whose principal aim is “to ensure the safe handling, transport and use of living modified organisms resulting from modern technology that may have adverse effects on biological diversity, taking also into account risks to human health” [2]
This protocol entered into force during September 2003, and it currently has 170 parties (167 United Nations member states, the State of Palestine and the European Union) [3]. However, other countries such as the United States of America, Canada and Argentina have not signed this agreement.
This protocol states in its Article 18 [4] (Handling, Transport, Packaging and Identification) the suggested documentation associated with the shipping of transboundary shipping of GMOs in order to avoid adverse effects. Such documentation includes:
- Identify them clearly as Genetically Modified Organisms
- Specify any extra requirements for the safe shipping
- Include the contact information to whom the GMOs are consigned
Transatlantic regulations
Secondly, we started to look for the current international legislations and guidelines for the transatlantic shipment of GMOs.
We found out that such shipment is not regulated by just one International Institution, since countries around the world follow different legislations and guidelines between each other; for example, most European Countries, as mentioned above, follow the guidelines suggested by the Cartagena Protocol on Biosafety, however, some countries such as the United States, Argentina, Canada, posses their own legislations for the shipment of GMOs.
Despite the fact that the legislations and guidelines between countries may be different between each other, e.g. Parties and No-Parties of the Cartagena Protocol on Biosafety, the World Health Organization, an international and neutral Institution, launched in 2015 the Guidance on regulations for the Transport of Infectious Substances 2015-2016 [5] to “provide practical guidance to facilitate compliance with applicable international regulations for the transport of infectious substances and patient specimens by all modes of transport, both nationally and internationally”
CryptoGErM must take into account, those three different guidelines and regulations to ensure that the Bacillus subtilis spores containing the encrypted information can be sent freely nationally and internationally.
Consulting national and international regulations, we ensure that CryptoGErM obeys the legal standards for the shipping of GMOs

According to the guidelines from the World Health Organization, the Bacillus subtilis spores used in CrytpoGErM are classified in Class 9 and assigned to UN 3245 since they “do not meet the requirements of infectious substances but are capable of altering animals, plants or microbiological substances in a way which is not normally the result of natural reproduction”
“Bacillus subtilis spores used in CryptoGErM are assigned to UN 3245 for their shipping”
GMOs assigned to UN 3245 must be shipped by following the Packing Instruction P904 [6]. This instruction states the requirements for the container used in the shipping of GMOs:

- An inner package: Primary receptacle and secondary packaging, must be leakproof for liquids or siftproof for solids. In case that the sample is liquid, absorbent material must be placed between the first and secondary packaging
- An outer packaging shall: Strong enough for its capacity, mass and intended use
These requirements are explained graphically in Figure 1 from the “Guide to Shipping Biological Materials” [7] document from the North Carolina University (NCSU). Please refer to this document for graphical consultant of the shipping
However, CryptoGErM found out that the labelling in the transatlantic shipping is not common since the legislations for the transboundary shipping are rather different between countries in America and those in the European Union.
This is particularly true for the Parties and Nonparties of the Cartagena Protocol, whose regulations and legislations are rather different. In order to solve problems that might occur between those parties, it is stated in the Cartagena Protocol that “Parties may enter into bilateral, regional and multilateral agreements to avoid potential conflicts”
We sent the spores of Bacillus subtilis with the encrypted message to the Wageningen UR Team and iGEM TU Eindhoven through the facilities of the University of Groningen to ensure a secure and safe shipping.

Sending of ours spores to Wageningen and Eindhoven!!!!
References
- [1] Regeling van de Staatssecretaris van Infrastructuur en Milieu. (July 7th, 2016) Retrieved from Regeling Genetisch Gemodificeerde Organismen Milieubeheer 2013. http://wetten.overheid.nl/BWBR0035072/2016-07-01#Hoofdstuk1
- [2] Convention on Biological Diversity. (August 15th, 2016) The Cartagena Protocol on Biosafety. Retrieved from https://bch.cbd.int/protocol/
- [3] Convention on Biological Diversity. (June 6th, 2014) Parties to the Protocol and signature and ratification of the Supplementary Protocol Retrieved from https://bch.cbd.int/protocol/parties/
- [4] Convention on Biological Diversity. (July 16th, 2016) Text of the Cartagena Protocol on Biosafety. Retrieved from https://bch.cbd.int/protocol/text/
- [5] World Health Organization. (January 1st, 2015) Guidance on regulations for the Transport of Infectious Substances 2015-2016. Retrieved from http://apps.who.int/iris/bitstream/10665/149288/1/WHO_HSE_GCR_2015.2_eng.pdf
- [6] UN3373 medical packaging. (June 2016)
- [7] North Carolina State Universuty. (28 September, 2016) Guide to Shipping Biological Materials. Retieved from https://www.ncsu.edu/ehs/dot/Bio_shipping.pdf
Education
“Science is fun. Science is curiosity. We all have natural curiosity. Science is a process of investigating. It’s posing questions and coming up with a method. It’s delving in” - Sally Ride
In our survey we encountered some worrying results. Namely the fact that 26% of the participants did not know what bacteria are. This is something that alarmed us. It became clear that informing people about synthetic biology was the key for making the world ready for CryptoGErM.
The best way to do this, was through education. So, in collaboration with ScienceLinX, we organized a day at the betafaculty. On this day 115 high school students came to visit us at the campus to learn about our project and about synthetic biology. We did not only invite students with an affinity for biology, but all kinds of students. We did this because we strongly believe in the cooperation between fields to make projects stronger and to provide a fresh view on problems.
The students and chaperoning teachers attended a lecture in which they learned the basics of synthetic biology, followed by a lecture about our own project. Herein we stressed the fact that we are a very diverse team and that students with almost every background can contribute to the iGEM competition. The discussions following this lecture did not only prove the interest that the students showed in the project, but were also very helpful to us. These lectures pushed us to explain our project as clearly as possible, while still including enough detail to stay true to the complexity of the project.


In addition to the theoretical lectures, we gave the students some experience in a real lab. Because we only had one hour in the lab, we decided to do some bio-art. This would teach them how to work with an inoculation loop and agar plate and to give them nice visualisation of lab work with bacteria. Dr Jan Kiel kindly provided us with different coloured micro organisms. Because we worked with different strains that had no antibiotic resistance, we taught the students how to work sterile, by using a flame.
Besides these general educational activities, we wanted to go a little more in depth with some of the students. Therefore we invited some high school students to do their practical work for their high-school thesis, and learn some basic cloning techniques. Because we only had a few days, we could not go through the entire process of bio-encryption. But they had some interesting sub questions we could answer. A few students were interested in which organism to use. To investigate this we cloned sfGFP in both Bacillus subtilis and Escherichia coli. We found that E. coli was harder to work with, because it does not have natural competence. Both E. coli and B. subtilis showed fluorescence, which means that the students succeeded in their first cloning!


In the Netherlands, high school students choose a specialisation when they are half way into their six year program. This can be economical or focused more on technology and health. At the end of their studies they work on an end project for about half a year. Herein they demonstrate the knowledge and skills they acquired over the years. For the more beta oriented students, this includes experimental work.
Student Celine about her experience:
“I worked a week during the summer for my high school thesis at the RuG. One of my questions in my thesis was which bacteria is better for inserting a plasmid. To research my question I worked with two students of the iGEM Team and cloned a plasmid with GFP in both bacteria. We grew B. subtilis overnight and then transformed it with the plasmid. With E. coli we first had to make competent cells and after that we did a heat shock transformation.
My time in Groningen was very interesting. I saw and learned a few new things, where I normally not get in touch with. The students were very nice and answered all of my questions. It was a successful week!”
Students Mayra & Robyn:
Mayra and Robyn are doing their high school thesis on cryptography in bacteria and they also followed a few days in our lab to experience working with bacteria, especially inserting a part in bacteria.
“Thanks to the iGEM Team we got further in our research for our high school thesis. We learned a lot in these three days. It was very nice to work in a lab.”


Students Marco, Jarko & Daniel
Marco, Jarko and Daniel also did their project about cryptography in bacteria. They already discovered that there are several ways in order to leave a message in a bacterium. For example, they have read that you can make a color-coded bacteria, when they come in contact with a substance, such as an antibiotic. By allowing bacteria to change color through a certain substance, you can use the bacteria as a secret ink. They also found that combinations in the DNA itself can give a meaning, such as a letter or number. By then to put this combination in the DNA you get a kind of secret language in the genome, which you can read by mapping the DNA and translate. Marco, Jarko and Daniel came in our lab to discover what it is like to change something in DNA of bacteria. The same as the other students they cloned GFP inside E. coli and B. subtilis.
“The days were a few learn full days, but also fun. The explanations were clear and we were helped good. In this combination our experiment was a success!”
Students Lieke, Anouk & Imke
Lieke, Anouk and Imke are currently busy with their high school thesis about GFP in guppies. Since we, as iGEM Team, are not allowed to work with animals, we invited them to clone GFP in bacteria.
“During our days in the lab of Groningen we learned a lot, we really liked to clone GFP in bacteria and the program was well arranged. The help was good and kindly. We learned a lot of this experience, it also was fun to do.”









